Computer Registration Portal
A vast number of mobile computing devices connect to the university network every day, creating a challenge in maintaining the availability, performance, and security of our network. To ensure “everywhere, anywhere” connectivity, we allow any mobile device – laptop, smartphone, tablet, etc. – to connect as long as the user is authenticated using their university username and password. In addition to university-owned devices, we support a “Bring Your Own Device” (“BYOD”) opportunity to access university resources through your personal mobile device.
These mobile devices, both university-managed and personal, can take unintentional advantage of the open nature of our network availability. Once connected to our network, these devices can spread malicious software to other connected systems, or can act as a pathway through which intruders can attack our sensitive resources. Because these devices are so mobile, they move freely within the university and can be difficult to locate.
To allow us to provide a safe and secure computing environment, Information Management and Services (IMS) is deploying an additional authentication method to detect and protect all devices connecting to the university network.
When first connecting your personal device, or any computer/mobile device that is not a member of the university's domain, you will be redirected to a new Computer Registration Portal. This one-time registration process uses your standard UT Health San Antonio username and password and will allow us to identify your device as a trusted source before gaining access to university resources.
Frequently Asked Questions
- What is the Computer Registration Portal?
- To whom does this apply?
- To whom does this not apply?
- What happens after I register?
- Where can I download the KACE management agent?
- Is my computer going to be monitored?
- How does this help me?
- How does this benefit the University?
What is the Computer Registration Portal?
The portal is a one-time login used to register computers, smartphones and tablets to the university's network the first time they connect.
To whom does this apply?
The portal applies to uncontrolled systems, such as personally-owned devices or those owned by the university that do not have the KACE management application installed. If your computer is not registered under the university domain (uthscsa), it is likely you do not have the KACE management agent installed.
To whom does this not apply?
- Wireless devices connecting to the HSCGuest WiFi network
- Servers
Note: If you have a server you believe resides on the same subnet as your workstation, please notify the Service Desk immediately to minimize any service disruption. The Service Desk can be reached by phone at 210-567-7777, or by email at ims-servicedesk@uthscsa.edu
What happens after I register?
- Faculty and Staff: A notification will be generated and delivered to your email address confirming your registration and providing you with instructions to download and install the KACE management agent. (Note: opting out of installing the KACE management agent will cause you to register your computer frequently.)
- Students: No further action is required. You have registered your device.
Where can I download the KACE management agent?
You can download and install the KACE management agent by selecting one of the links below.
- Windows -- download instructions (PDF) -- download installer
- Mac -- download instructions (PDF) -- download installer
- Linux
Is my computer going to be monitored?
No. This tool does not have the capability to monitor your computer use. The portal is designed to only detect and track who and what connects to the university network.
How does this help me?
If computers become compromised, either by malware or by intruders, IMS will first work on computers they can positively identify, while queuing others up for service. Registered devices can easily be identified and their users notified, reducing the amount of time the device is out of service.
How does this benefit the University?
The Computer Registration Portal system will:
- Detect when an uncontrolled device connects to the university network; unregistered devices will have no access to the university's network or its information resources. This will prevent intruders from gaining access by secretly connecting a computer to our wired or wireless network;
- Deliver the KACE management agent to computers not currently joined to the university's domain;
- Determine if the attached device belongs to a student or an employee, and configure network access appropriately; and
- Build a comprehensive inventory of active devices connecting to the university's network
The comprehensive inventory and the KACE management product will allow the university to respond more quickly to intrusions and compromised computing devices, resulting in faster turnaround times getting systems back up and running and less down time for our customers.
Steps for Device Registration
1. Once the portal goes into service, if your device meets the criteria of the previous bullet, you will be prompted to login to the portal to register your device.
Important: If your computer appears to be disconnected from the network, open a browser and navigate to any ".com" website (e.g., "cnn.com"); this will launch the portal when the web activity is detected. If the portal does not come up, then please restart your computer.
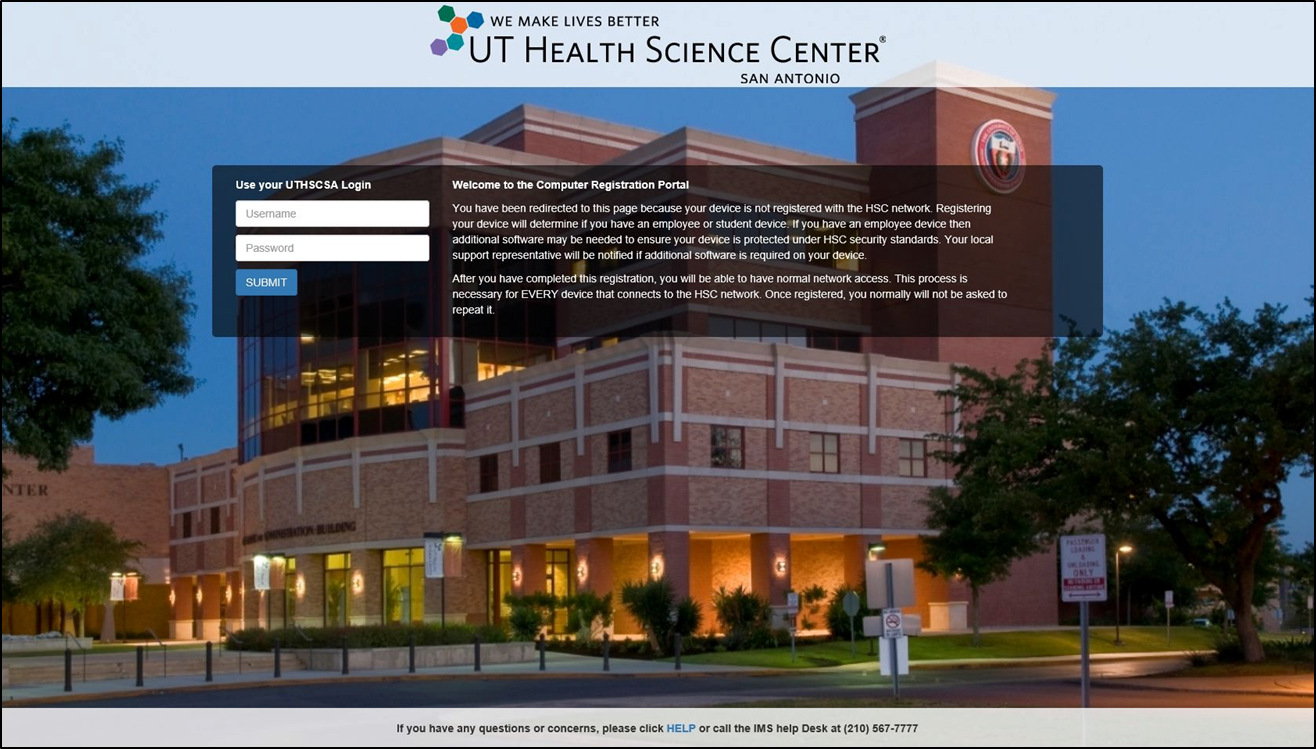
2. Enter your University domain credentials.
- Enter only your username, and do not include "uthscsa\" before or "@uthscsa.edu" after.
- Enter your password.
- Click the Submit button.
3. The registration process will begin.
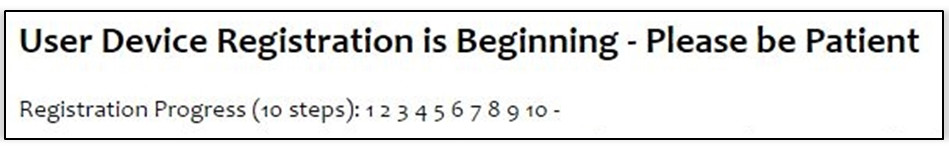
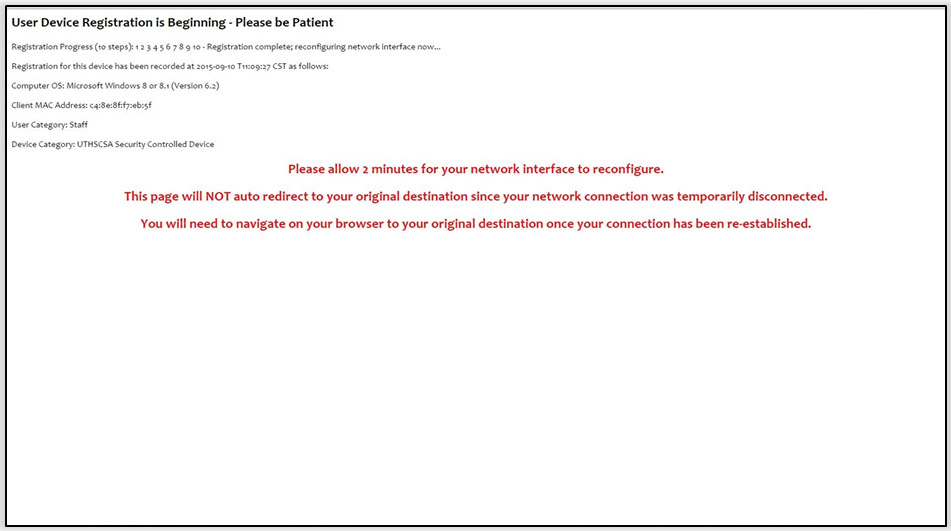
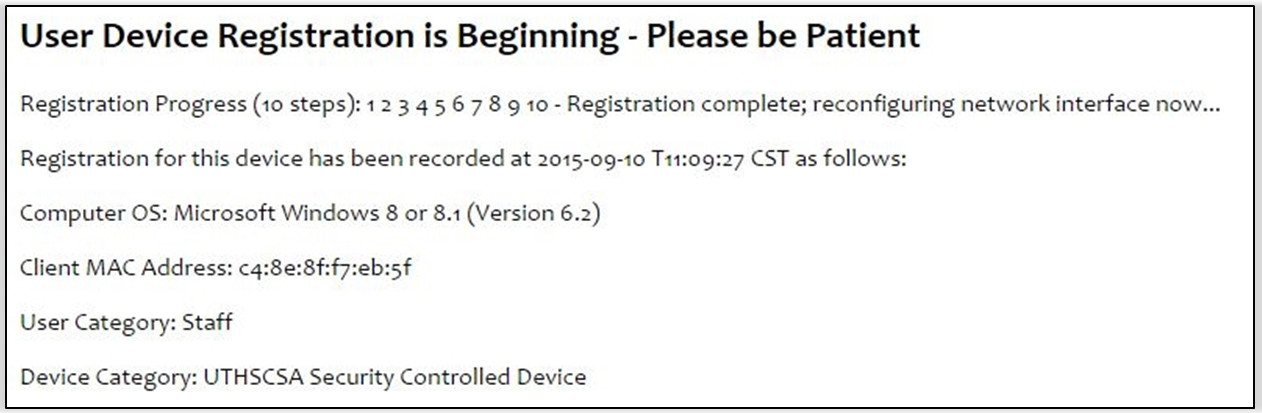
When complete, the page will display the following:

4. The page will then update to display the information gathered; this is the only information the portal stores to identify your computer, smartphone, or tablet. If you use a computer that has both wired and wireless connections, the portal will register each connection the first time it is used.
5. The total process will take approximately 2 minutes. The registration portal will not redirect you to your original destination, so after this time, you will have to re-enter the address of the site you want to visit, or you may close the browser.

6. You can now browse the network and access university information resources.